Of Ransomware, Hackers, FTC and HIPAA
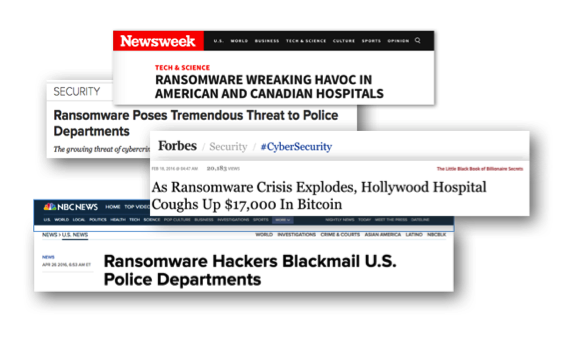
You’ve seen it … you’ve heard it … you couldn’t miss it!
Health care facilities have been victimized by hackers who steal patient identities and increasingly disable access to key patient treatment and status records until ransom demands are met. Additionally, employees may suffer because of a workplace breach of their confidential information.
Traditional technology networks are generally vulnerable and lucrative to attack. ASCs as well as small to medium-size hospitals are marked as primary targets for breaches because their security infrastructure is often lacking. That underscores a July 2016 report that revealed that the healthcare industry is hit significantly harder by ransomware hackers than any other sector … to the tune of 88% of attacks targeted hospitals.
In this article, we’ll take a look at what are current threats as well as those to be anticipated based on advances in medical technology. Additionally, we’ll review technical safeguards under HIPAA regulations and employer responsibilities as viewed by the Federal Trade Commission (FTC).
Healthcare as Prime Targets for Hackers
ASCs, hospitals and other healthcare facilities are primary targets for the bandits. In addition to the lure of potentially vulnerable cyber-infrastructure, healthcare facilities maintain a treasure chest of patient data.
The bad guys can have a field day once they obtain patients’ Social Security numbers, home addresses, bank account and medical information. Think of the mayhem this implies in using these thefts of identity to gain access to credit cards, obtain loans or raid financial accounts.
Cyber attacks will likely accelerate as there is more potential to steal sensitive health data … often viewed by the thieves as even more valuable than financial information that is the usual target of identity theft.
Ransomware
Ransomware is malware (malicious software) that locks computer systems and prevents access to data until a ransom is paid.
To put the severity of these acts in perspective, it is estimated that there are over 4,000 ransomware attacks daily with healthcare as the largest target. And a Kapersky Lab products report pegs ransomware attacks at an 11.4% increase over last year.
The payoff for the bad guys is often data held hostage for ransom to be paid by the hospital to the bandits. Last year both Hollywood Presbyterian Medical Center and MedStar Health were victimized. The MedStar hack affected all 10 MedStar hospitals in D.C. and Maryland. Its approximately 250 clinics were hacked and paid significant dollars to the cyber-attackers.
As an example of the havoc this can cause, one spouse of a MedStar cancer patient reported her husband’s daily treatments were disrupted by the hack including cancellation of scheduled appointments.
Those are tough alternatives … rebuilding networks which may mean shutting down many or all hospital facilities, or pay the ransom which sends the message that hospitals are willing to pay hackers to reinstate access to their data and computers.
Employer Liability for Identity Theft
Employers must take reasonable steps to protect sensitive employee information. Files and computers with key identifiers such as social security number, address, date of birth, etc. should be guarded and accessible only by authorized persons.
This advice is further underscored as essential in light of an increasingly aggressive posture by the Federal Trade Commission (FTC) in dealing with how employers protect sensitive information … both from external hackers as well as internal staff.
ASCs, hospitals and other healthcare providers that meet the rule’s definition of “creditor” must abide by the Red Flags Rule and develop and implement a written identity theft prevention program. The rule is broadly written and may well apply to virtually all or at least many healthcare facilities. Note: The ultimate responsibility for compliance is the business owner(s) or senior officer charged with that duty.
According to a recent MediaPro survey only 28% of healthcare employees demonstrated the privacy and security awareness to prevent incidents of a breach. This, coupled with an increase in breaches by “insiders” clearly demonstrates a need for better training and conformance to the safeguards mandated by the Red Flags Rule.
HIPAA Weighs In
Over fifteen years ago, the Department of Health and Human Services (DHS) implemented technical safeguards to protect electronic protected health information and control access to it, the HIPAA Security Rule. The Security Standards for the Protection of Electronic Protected Health Information (the Security Rule) establish a national set of security standards for protecting certain health information that is held or transferred in electronic form.
The Rule allows a covered entity to use any security measures that allows it reasonably and appropriately to implement the standards and implementation specifications. Understanding the basics will significantly assist healthcare organizations determine the security measures appropriate for their facility.
There are five principal HIPAA Standards:
- Access Control
- Audit Controls
- Integrity Controls
- Person or Entity Authentication
- Transmission Security
As you likely expect, there are penalties for non-compliance.
Healthcare leadership must continually become more diligent in identifying network vulnerabilities and take steps to remedy weaknesses through increased cybersecurity and aggressive data backup protocols. Anything less exposes patients, employees, management and institutions to exceptional penalties at the hands of both hackers and regulators.